The sudden and total collapse of the digital infrastructure at one of the world’s most prominent medical technology firms has sent shockwaves through the global healthcare supply chain this week. Stryker, a Fortune 500 leader responsible for critical surgical equipment and medical devices, found itself paralyzed after an unprecedented cyberattack successfully compromised its internal Microsoft environment. This breach did not merely slow down operations; it effectively severed the digital arteries that allow the company to function on a global scale. From the immediate cessation of electronic ordering to the complete shutdown of shipping and customer support portals, the impact was felt instantaneously across international borders. Manufacturing plants were forced to halt production as the lack of digital coordination rendered assembly lines useless. This incident serves as a stark reminder that even the most robust organizations remain vulnerable to sophisticated actors who understand the interconnected nature of modern enterprise software. As the chaos unfolded, hospital administrators and surgical teams were left wondering how such a massive failure could occur in an era defined by heightened cybersecurity awareness and significant investment in defensive technologies.
The Mechanics of a Digital Erasure
Exploiting Trusted Administrative Infrastructure: The LOTL Strategy
Security analysts monitoring the situation have pointed to a sophisticated “living-off-the-land” or LOTL technique as the primary driver behind the massive operational failure. Unlike traditional cyberattacks that rely on the deployment of recognizable malware or ransomware payloads, this method utilizes the legitimate tools already present within a corporate network to execute malicious commands. In the case of Stryker, the attackers managed to bypass standard perimeter defenses by gaining access to high-level administrative accounts. Experts from organizations like Cisco Talos suggest that these credentials were likely harvested from repositories on the dark web, allowing the threat actors to log in as authorized users. Once inside, they did not need to install a single piece of suspicious code to begin their campaign of destruction. By operating within the shadows of trusted administrative processes, the intruders remained undetected by traditional antivirus software, which is often programmed to ignore actions performed by verified system administrators using standard management tools.
The centerpiece of this destructive campaign involved the weaponization of Microsoft Intune, a cloud-based endpoint management solution designed to help companies manage and secure their fleets of mobile devices and laptops. After securing administrative control, the attackers triggered a “remote wipe” command that was simultaneously sent to thousands of corporate devices across the globe. This function, which is normally reserved for erasing data from lost or stolen hardware, was used to factory-reset workstations and mobile units on a massive scale. The result was a catastrophic loss of local data and the immediate bricking of essential hardware needed for daily business operations. Employees arrived at work only to find their laptops wiped clean, with no operating system or company software remaining. This specific choice of methodology highlights a terrifying shift in the threat landscape, where the very tools designed to protect and manage an enterprise are turned into instruments of systemic erasure, leaving IT departments with the monumental task of rebuilding their entire digital ecosystem from scratch.
Geopolitical Motivations: The Role of Targeted Sabotage
Responsibility for the attack has been claimed by a group known as Handala, an Iranian-aligned threat actor that has recently increased its focus on Western infrastructure and high-value corporate targets. This group did not appear to be motivated by the traditional financial gains associated with ransomware, as there were no public demands for payment or negotiations for decryption keys. Instead, the motivation cited by the attackers was explicitly political, pointing toward Stryker’s ongoing business relationships and contracts with the United States Department of Defense. This shift from cybercrime for profit to state-aligned sabotage marks a significant escalation in how private corporations are viewed as legitimate targets in broader geopolitical conflicts. By targeting a company that provides critical medical infrastructure, the attackers were able to cause maximum disruption not just to a single business, but to the broader healthcare delivery system that relies on a steady flow of surgical supplies and medical maintenance.
The strategy employed by Handala suggests a deep understanding of the psychological and operational impact that a total digital blackout can have on a global corporation. By choosing to wipe devices rather than encrypt them, the attackers ensured that the recovery process would be slow, manual, and incredibly expensive. There is no shortcut to restoring a device that has been factory-reset; each unit must be physically or remotely re-imaged and re-configured, a process that can take weeks for a company with tens of thousands of employees. Furthermore, the public nature of the claim and the stated reasons for the attack serve as a warning to other firms operating in the defense and technology sectors. This incident demonstrates that maintaining a secure posture now requires more than just technical defenses; it necessitates an understanding of a company’s geopolitical footprint and the potential for becoming a proxy target in international disputes. The attack was not just a breach of data, but a calculated move to degrade the operational readiness of a key industrial player.
Managing Crisis in a High-Stakes Environment
Safeguarding Patient Care: Isolation as a Primary Defense
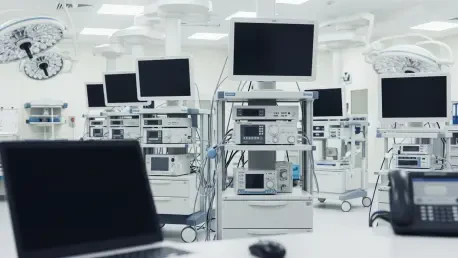
Amidst the chaos of the internal corporate shutdown, the primary concern for the healthcare community was the potential compromise of life-saving medical devices used in operating rooms and emergency departments. Fortunately, a central theme of the response has been the continued safety and functionality of the medical products themselves, which remained insulated from the corporate network breach. Stryker confirmed that its surgical visualization platforms, endoscopy tools, and emergency response equipment continued to operate without interruption. This resilience was achieved through a deliberate architectural design that separates the company’s internal business environment from the software ecosystems that manage its medical hardware. Because these devices often run on independent protocols or are housed on isolated hospital networks that do not communicate back to Stryker’s internal Microsoft servers, the remote wipe commands triggered by the attackers had no path to reach the clinical tools.
The separation of these environments proved to be the most critical factor in preventing a corporate disaster from becoming a public health crisis. For instance, smart beds and advanced stretchers utilized localized security protocols and independent communication channels that were never integrated into the central endpoint management system targeted by the hackers. This practice of network segmentation is a fundamental principle of modern cybersecurity, yet its real-world validation during this attack provides a powerful case study for the entire medical technology industry. Had the medical devices been directly linked to the corporate Intune environment for updates or monitoring, the impact on patient safety would have been catastrophic. Instead, surgeons were able to continue using Stryker’s cameras and specialized tools with confidence, knowing that the digital paralysis affecting the company’s billing and shipping departments did not extend to the sterile field of the operating theater or the critical care unit.
Resilience and Restoration: The Shift to Manual Coordination
To mitigate the impact of the digital blackout on hospital operations, the company was forced to revert to manual workarounds that harkened back to a pre-digital era of logistics. Sales representatives and field technicians took on an expanded role, coordinating directly with healthcare providers via personal communication channels to ensure that supplies reached their destinations. Since the electronic ordering and shipping systems were offline, the company had to rely on human intervention to track inventory and manage the distribution of essential surgical kits. This transition highlighted the importance of maintaining a decentralized and adaptable workforce that can continue to function when centralized platforms fail. While these manual processes were significantly slower and more labor-intensive than the automated systems they replaced, they allowed the company to maintain a baseline level of service for its most critical customers, preventing a complete breakdown of the medical supply chain.
The recovery effort focused heavily on the systematic restoration of the shipping and ordering platforms, which were prioritized over general internal communications. Technicians worked around the clock to rebuild the cloud infrastructure and re-establish secure links with distribution centers. The company also ensured that standard communication channels, such as telephone lines and certain email environments, remained secure for customer use, allowing for a semblance of normalcy during the rebuilding phase. This incident provided valuable insights into the necessity of having robust, offline contingency plans for every aspect of a global business. The strategy evolved from a purely reactive stance into a proactive effort to harden administrative tools against future exploitation. By the time the systems began to come back online, the organization had implemented more stringent multi-factor authentication and restricted the use of powerful administrative commands, ensuring that a single compromised account could never again trigger a global wipe of the company’s digital assets.
Strategic Adjustments: Lessons for the Cyber Landscape
The restoration of global operations at Stryker was characterized by a meticulous, phased approach that emphasized data integrity and the verification of every restored endpoint. Information technology teams worked to re-image thousands of laptops while simultaneously auditing administrative logs to ensure that no residual backdoors remained within the Microsoft environment. This recovery process demonstrated that the speed of restoration must often be balanced against the absolute necessity of security to prevent a secondary breach. The company also shifted its focus toward the implementation of immutable backups and more granular access controls for its endpoint management tools. By documenting the exact steps taken by the attackers, the firm was able to contribute to a broader understanding of how LOTL techniques can be mitigated. These actions provided a blueprint for other Fortune 500 companies to evaluate their own administrative vulnerabilities and move toward a zero-trust architecture.
The experience led to a fundamental reassessment of how modern corporations manage their relationship with cloud-based administrative services. It became clear that the convenience of centralized management tools like Intune must be accompanied by rigorous oversight and localized fail-safes. Moving forward, the industry adopted more robust monitoring for administrative behaviors, specifically looking for anomalies in the execution of high-impact commands such as remote wipes. This event also underscored the importance of maintaining clear, transparent communication with stakeholders during a crisis, as the company’s ability to reassure hospitals about product safety was vital to maintaining trust. Ultimately, the incident served as a catalyst for a global shift in cybersecurity priorities, moving the focus away from simple malware prevention and toward the defense of the administrative core. Organizations learned that the greatest threat often comes not from a new virus, but from the unauthorized use of the very keys meant to keep the digital house in order.